Cold Boot Attacks — Coursework Study
Disclaimer
This document is a university coursework assignment, translated and summarized from the original German version using ChatGPT.
It is not peer-reviewed and not formally published.
Provided for educational and demonstrational purposes only.
Author: skull
Keywords: RAM (Random Access Memory), Proof of Concept (PoC), Side-Channel Attack, Cold Boot Attack, BIOS, RAM Dump
ABSTRACT
This coursework explores a specific side-channel attack: the Cold Boot Attack.
A proof of concept was attempted, examining the attack model, experimental setup, encountered problems, execution, and results.
I. INTRODUCTION
The Cold Boot Attack exploits the fact that data in RAM is not immediately erased after shutdown.
By cooling RAM chips, data remanence can be extended, making it possible to recover sensitive information (such as encryption keys) even after power loss.
This study attempts to reproduce the attack in a controlled lab setting.
II. ATTACK MODEL
A. Data Persistence in RAM
RAM contents remain for a short period after shutdown.
Unless the BIOS or OS clears memory, this creates a small window (seconds to minutes) in which recovery is possible.
B. Extending Persistence with Cooling
Cooling (via compressed air spray or liquid nitrogen) can significantly extend the retention period — from minutes to hours or even days [1].
For this coursework, simple compressed air spray (“canned air”) was used as a practical method.

C. RAM Transplantation
One approach is to move cooled RAM modules into another machine for dumping.
This increases attack complexity and requires careful hardware compatibility [2].
D. Booting Another OS
A simpler method: boot the original machine into a live USB OS and dump memory.
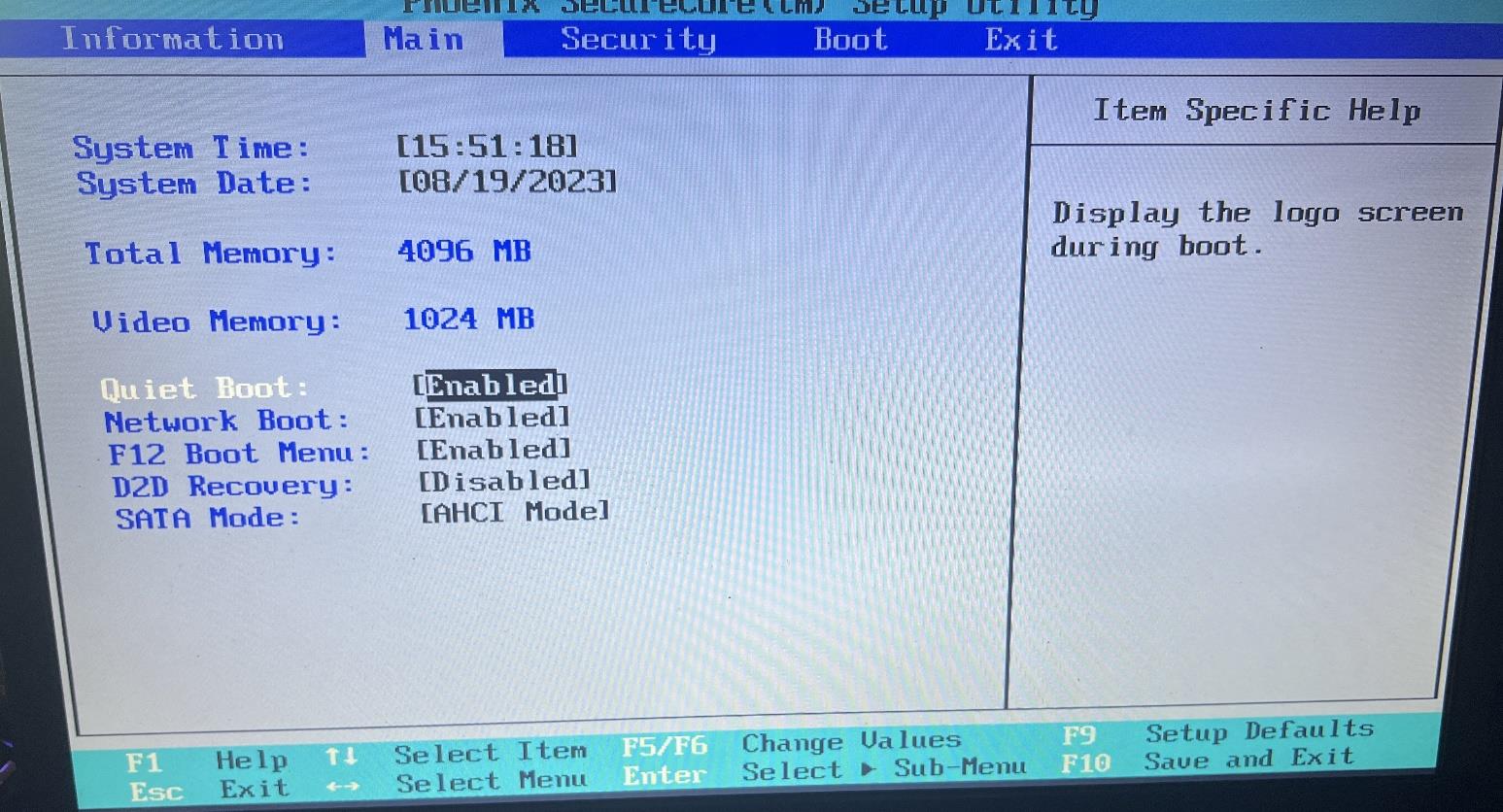
However, modern BIOS/UEFI often clear RAM at boot, complicating the attack.
Options like Secure Boot or Fast Boot must be reviewed.
E. RAM Dumping
Dumping requires pre-installed tools/scripts on the live USB to avoid RAM overwrite during boot.
F. Reading the Dump
RAM dumps can be searched with tools like strings and grep.
For example, keys, passwords, or known markers can be recovered.
III. EXPERIMENTAL SETUP
- Hardware: Old Acer laptop
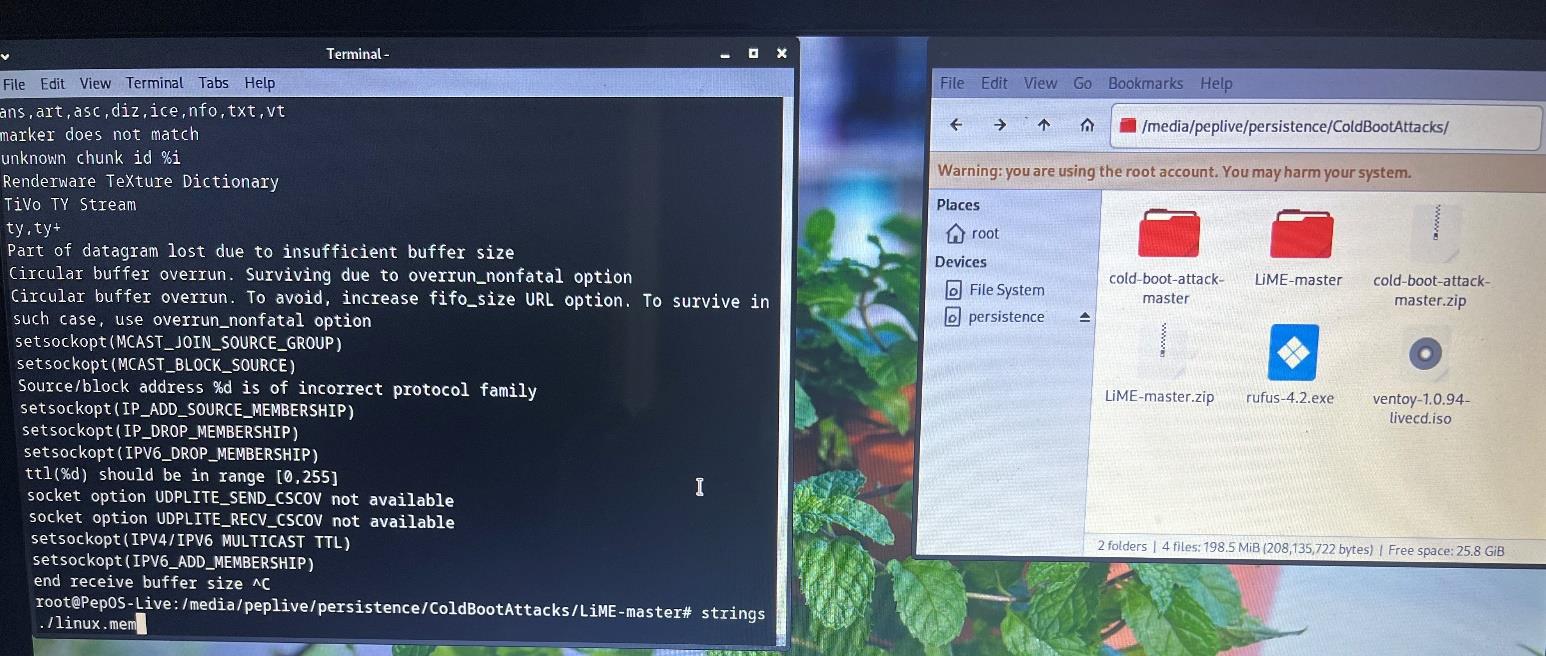
- OS: PeppermintOS live USB
- Tool: LiME kernel module for memory dumping
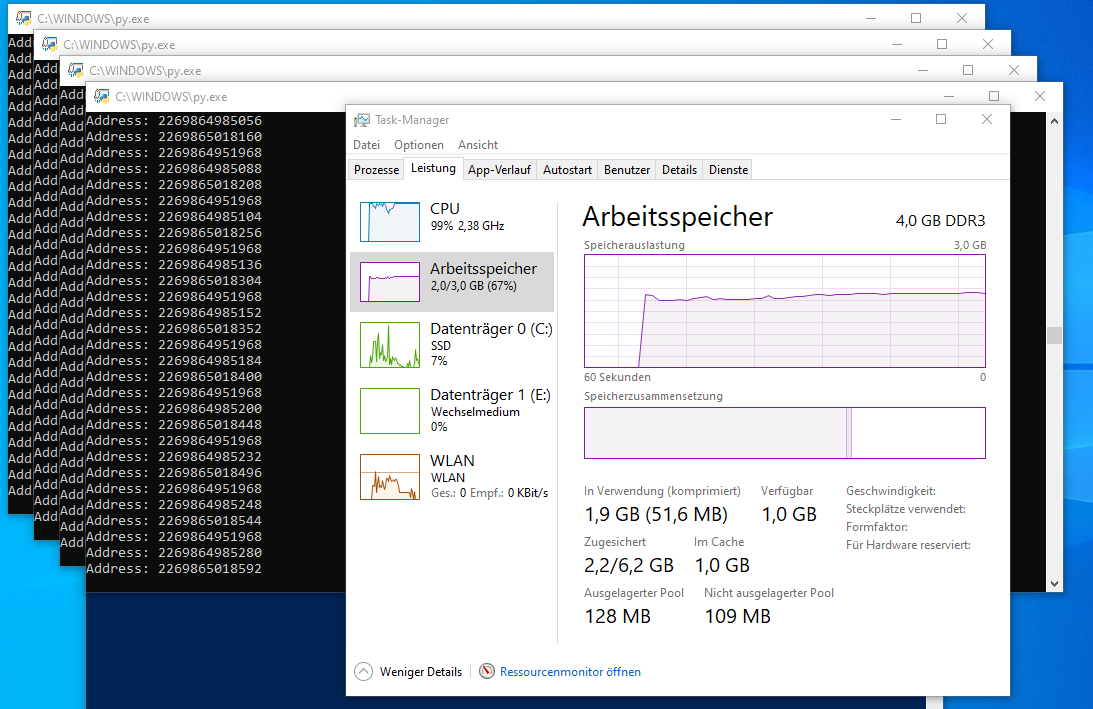
The goal: fill RAM with a known marker string (“funtimes”) before shutdown.
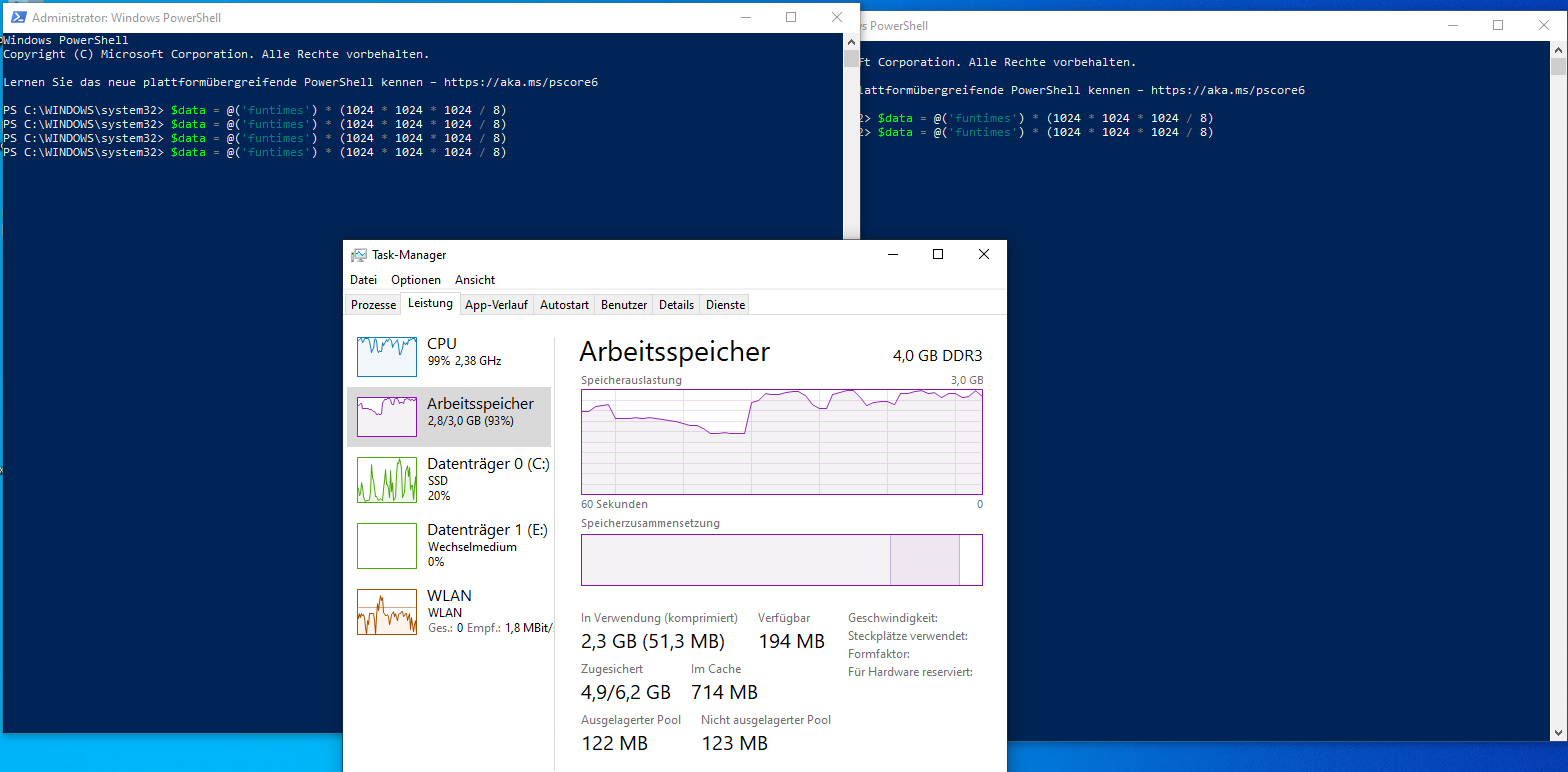
Initial attempts with Python failed due to memory optimization; PowerShell was used instead.
The system was force-powered off, RAM cooled with spray, and rebooted into the live OS.
LiME dumped memory, which was later searched with strings.

IV. CHALLENGES
A. Modern Defenses
Since 2009 [1], protections have hardened:
/dev/memaccess restricted in Linux- BIOS often clears RAM during boot
B. Tool Limitations
The tools described in the original paper failed to dump memory as expected.
C. Kernel Issues
Building a custom kernel with /dev/mem support failed on the live USB.
D. Success with LiME
The LiME kernel module ultimately succeeded in creating memory dumps.
V. EXECUTION
- Step 1: Fill RAM with “funtimes” using PowerShell.
- Step 2: Abrupt shutdown via emergency switch.
- Step 3: Cool RAM and reboot to live OS.
- Step 4: Dump RAM with LiME and search.
The proof-of-concept string was not recovered — likely due to BIOS memory clearing.
A working attack would require modified firmware, beyond the scope of this coursework.

VI. RESULTS
A. Feasibility
Cold Boot Attacks are possible but highly complex in practice.
They require system-specific preparation and careful timing.
B. Relevance
Still relevant as RAM encryption is not universal.
Forensics can use such methods to recover volatile evidence.
C. Mitigations
- Don’t leave systems unattended (on or off).
- Enable RAM encryption if supported.
- Use HSMs for key storage.
- Secure disk encryption with additional factors.
REFERENCES
- Cold Boot Attacks: Original Paper and Tools
- YouTube: RAM Transplantation
- Microsoft: WinDbg Documentation
- Microsoft: PowerShell Arithmetic Operators
- Accessing /dev/mem
- GitHub: LiME Cold Boot Attack
- Keeping Secrets in Hardware: Xbox Case Study (bunnie)
- HSM Presentation (SecAppDev 2010)
- Microsoft: BitLocker Countermeasures
For feedback or questions, contact: 📧 skull@ttl.zip